View Overview PDF Request Trial
VigorShield - Threat Protection
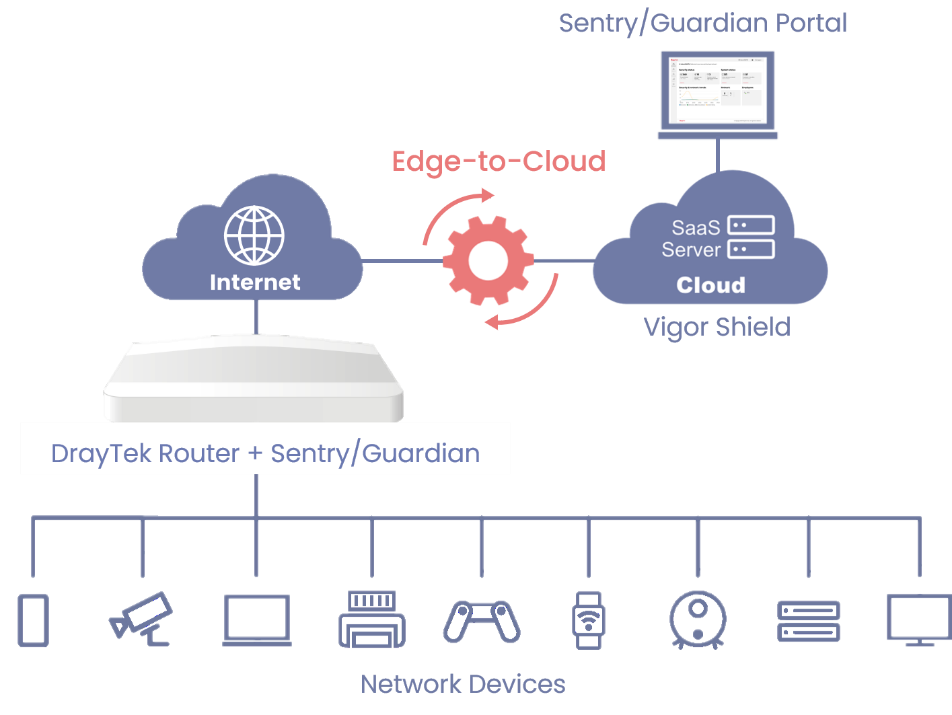
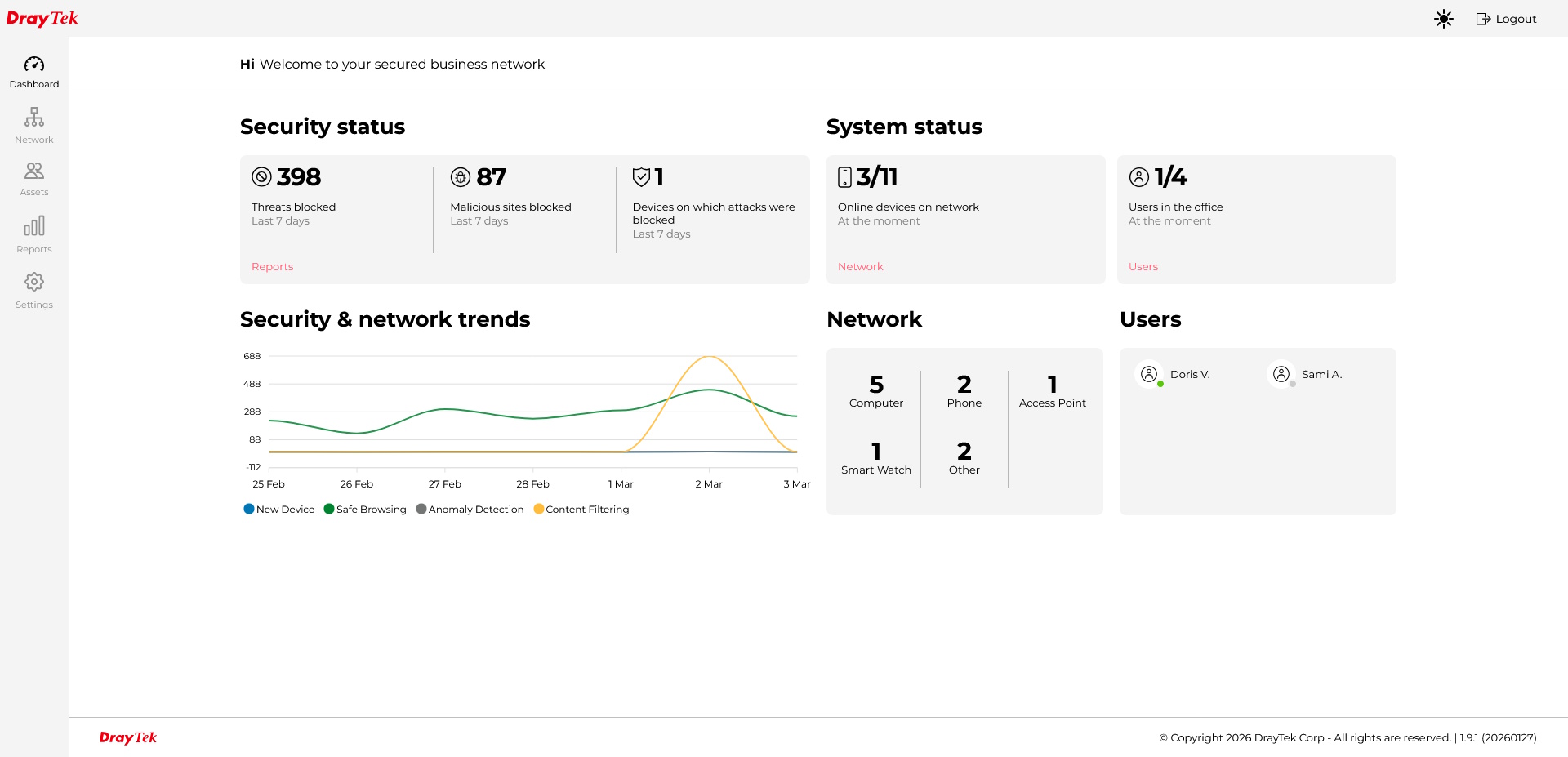
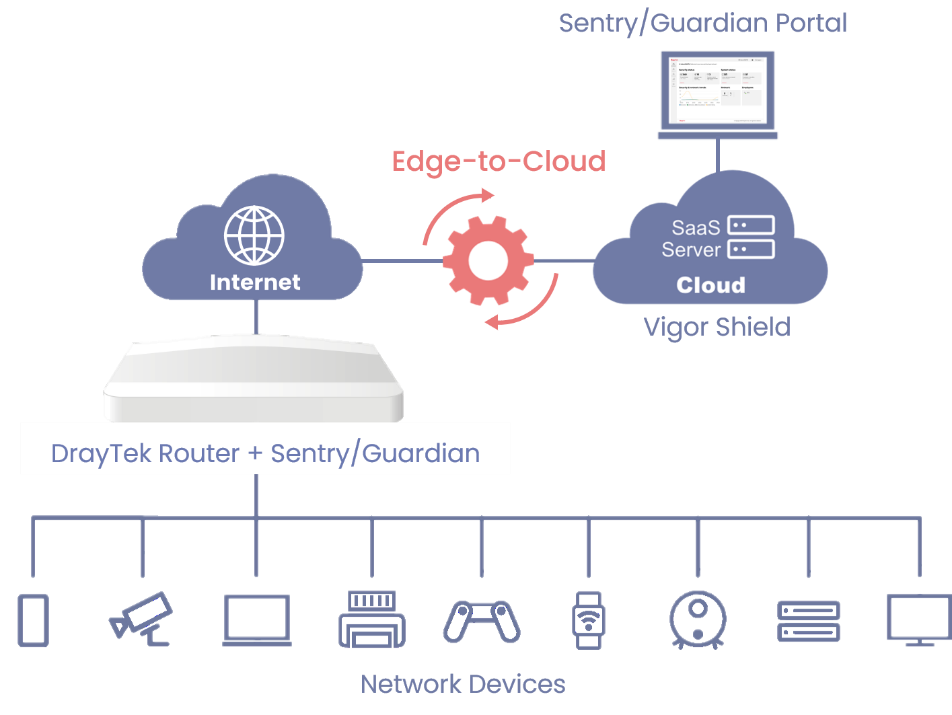
VigorShield is an intelligent cybersecurity solution designed to protect today’s mixed environments of laptops, smart devices, and unmanaged IoT/OT equipment. Built with advanced AI detection, network‑level protection, and virtual hot patching, it automatically identifies threats, blocks attacks, and keeps vulnerable devices secure even when they can’t be patched or updated.
Whether it’s a camera, Smart Plug, POS terminal, printer, medical device, or laptop, VigorShield continuously monitors every asset, learns normal behaviour, and intervenes instantly when something looks wrong. With no need for specialist IT skills, it brings enterprise‑grade protection to SOHO, prosumer, and SMB networks, stopping brute‑force attempts, IoT hijacking, vulnerability exploits, malware behaviour, and malicious communications before damage can occur.
In a world where IoT botnets and automated scanning tools make small networks prime targets, VigorShield delivers always‑on, fully automatic security. Powered by the most important device on the network – the DrayTek router.Product Overview
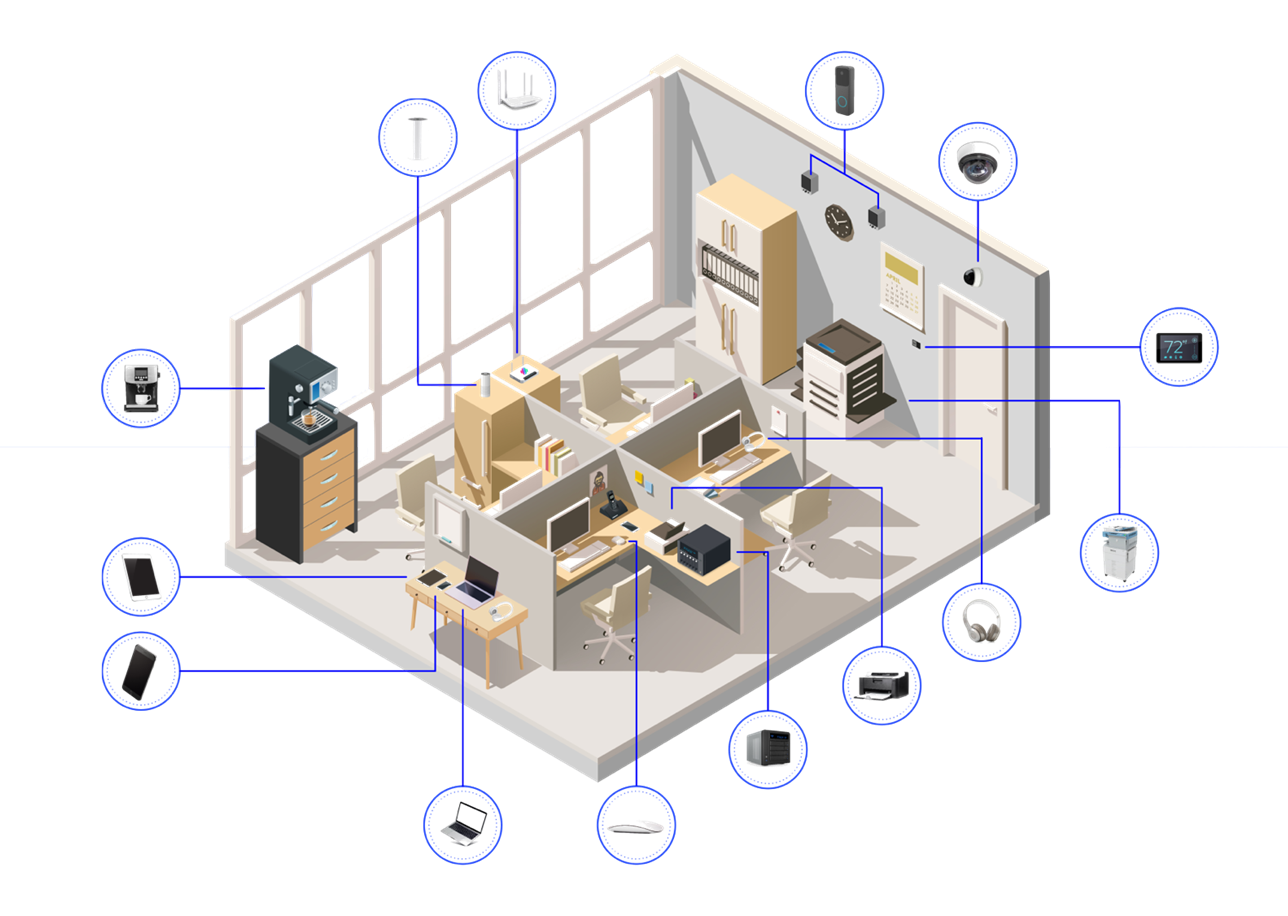
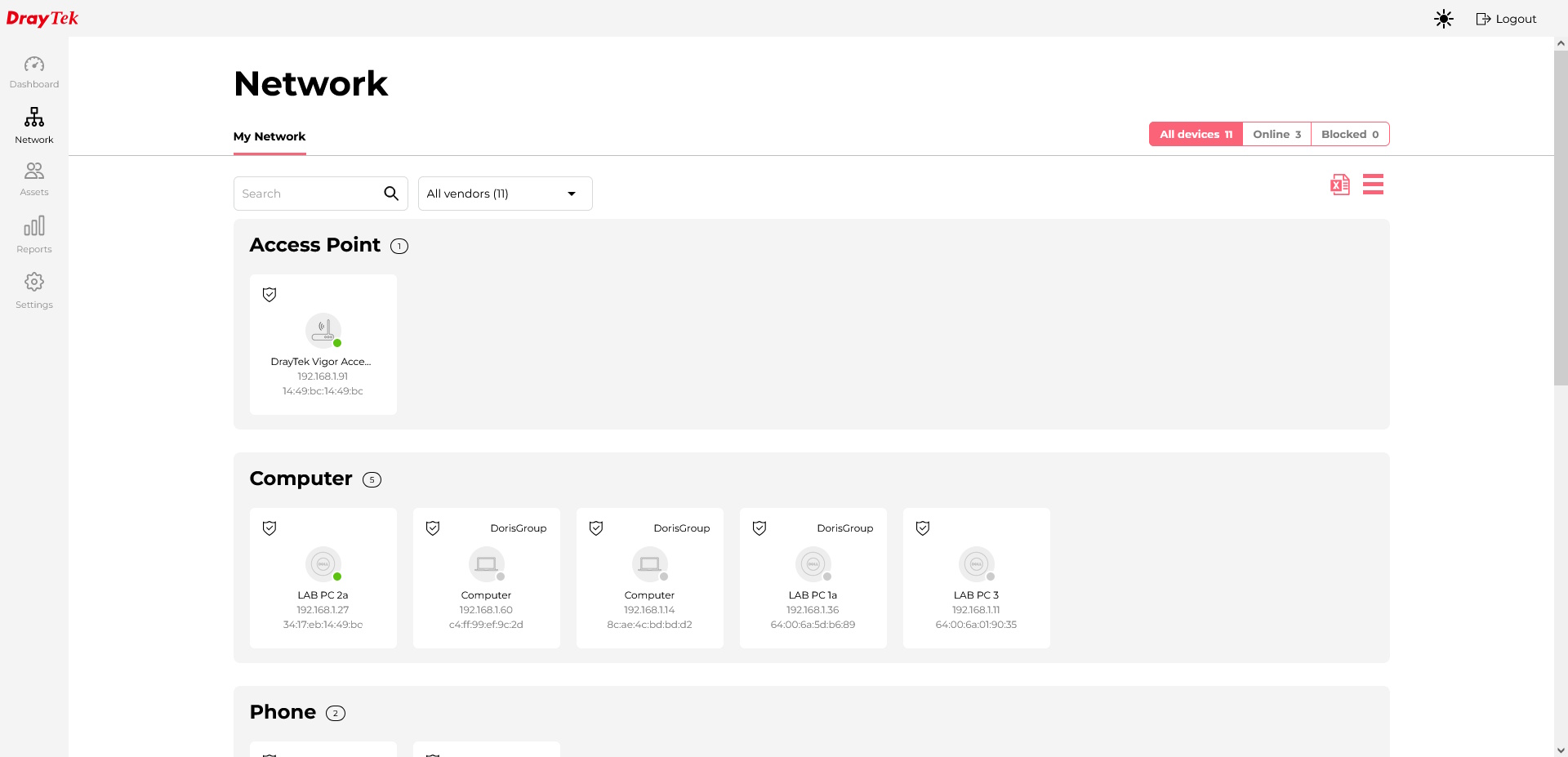
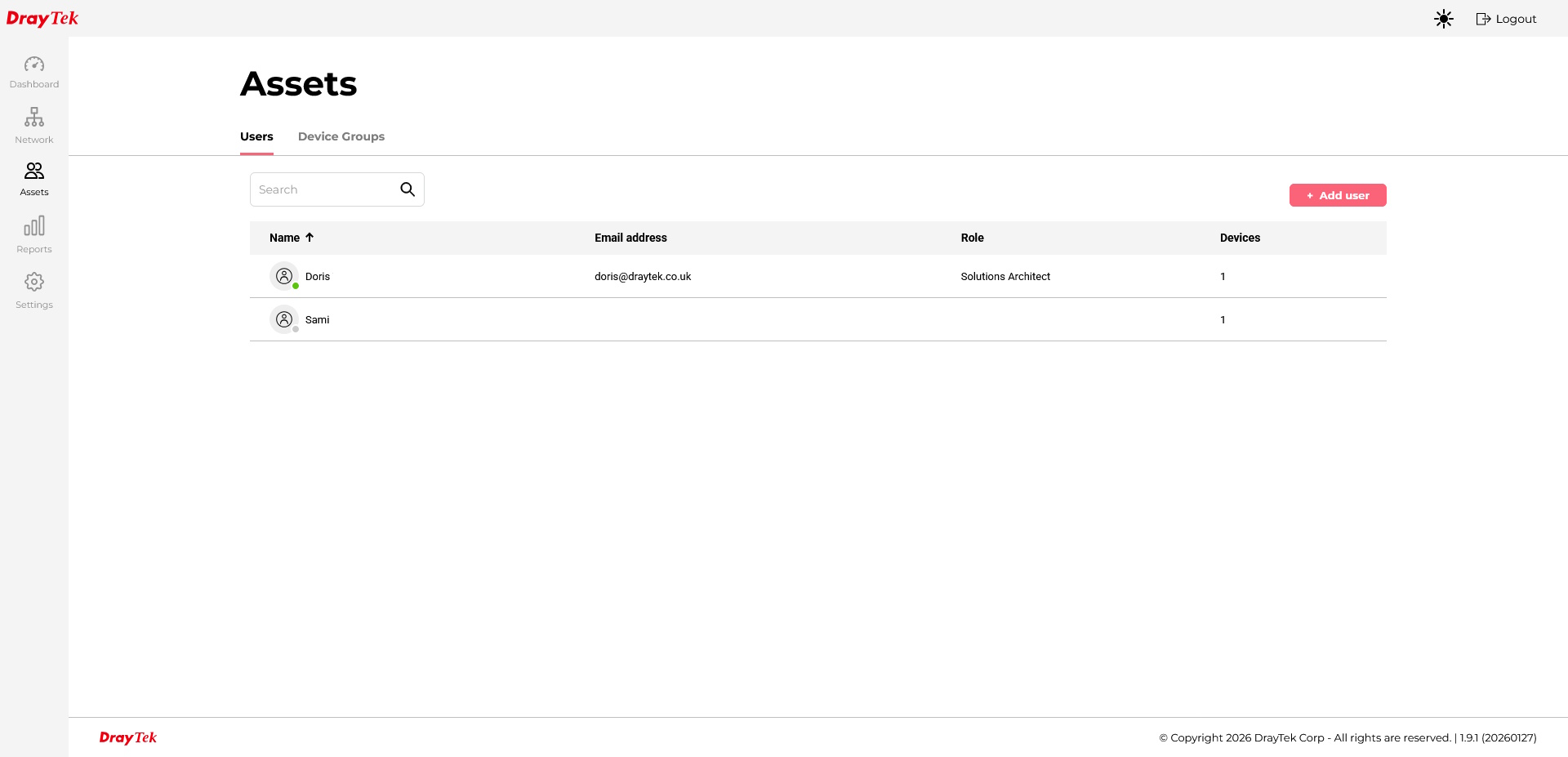
Automated Asset Visibility
Automatically discovers and fingerprints devices connected across your network, giving IT teams immediate visibility into what is online. Unknown endpoints are quickly identified and organised into manageable groups for easier monitoring and policy enforcement.
This reduces blind spots across branch offices, IoT deployments, and growing LAN environments while improving operational control.
Vulnerability Protection
Advanced DPI-based inspection helps detect and block exploit attempts, command-injection patterns, and malicious traffic before it reaches critical systems. This provides an essential layer of defence against known vulnerabilities and emerging threats.
It is especially valuable when software patches cannot be applied immediately, helping reduce exposure to CVE-related risks during patching delays.
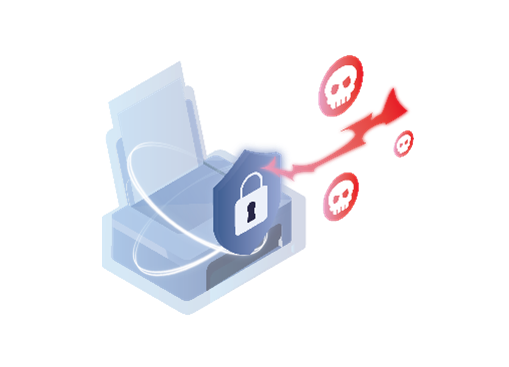

Agentless Coverage
Protect devices that cannot run endpoint software, including IoT, OT, and legacy infrastructure, without the need for additional agents. Security is enforced directly at the gateway, ensuring broad coverage across unmanaged assets.
This approach is ideal for hard-to-patch environments where traditional endpoint protection is not practical.
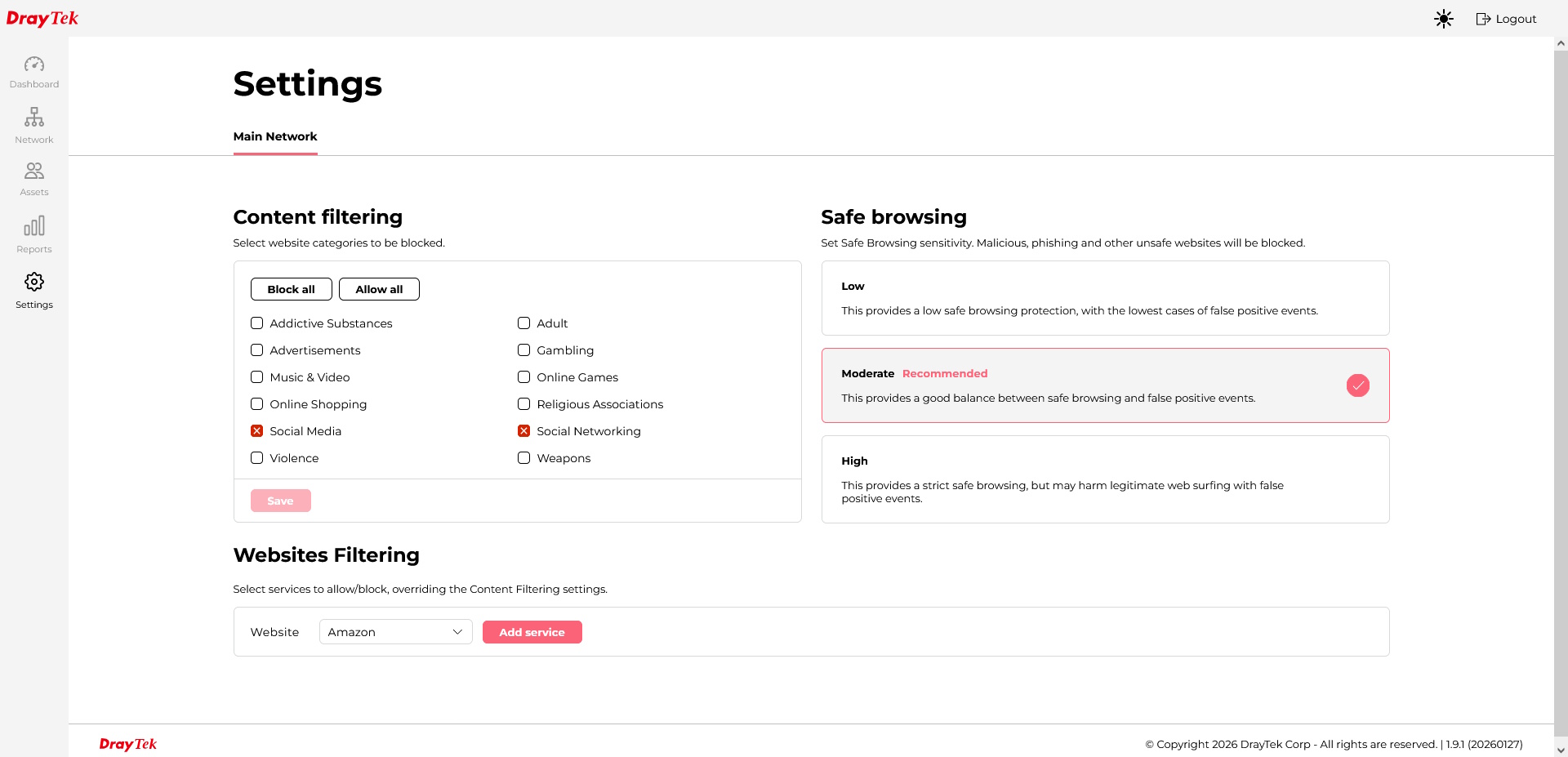
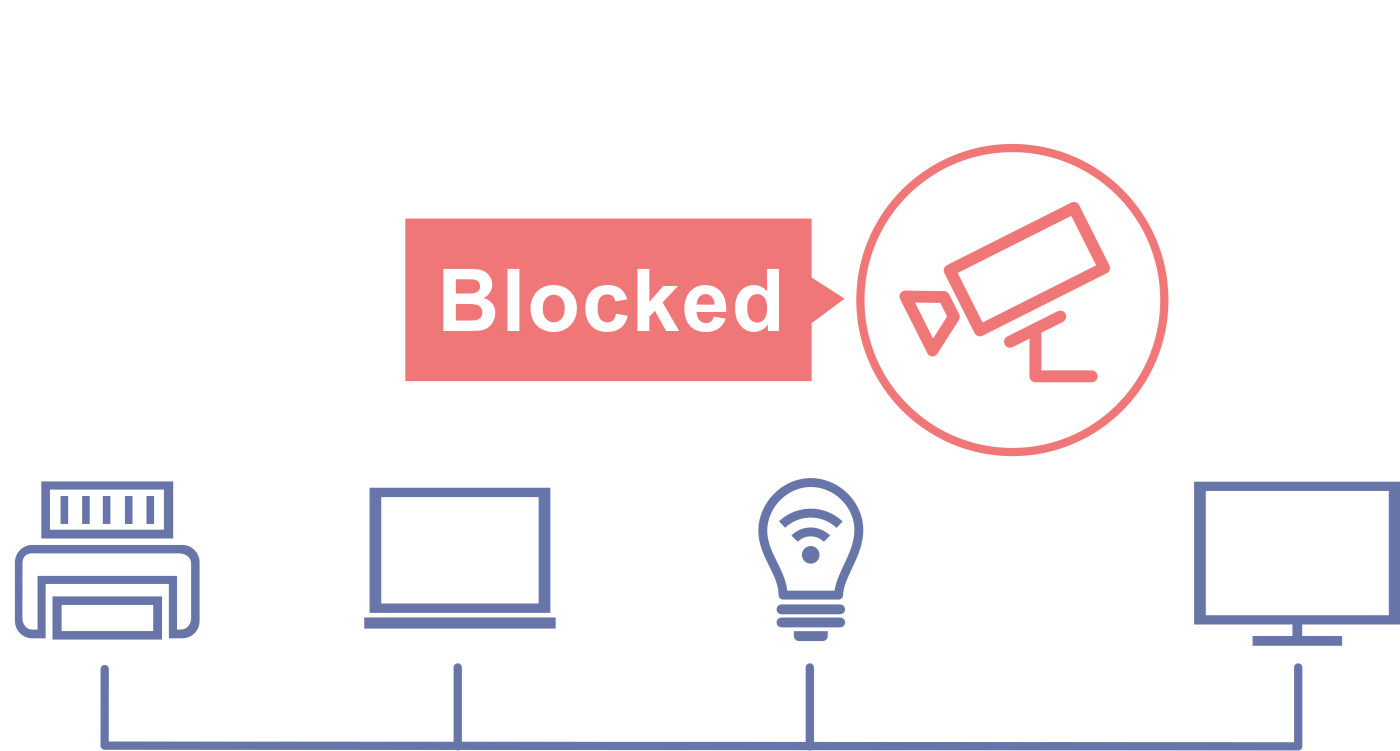
Least-Privilege Access
Apply access policies based on device type, role, or network segment to ensure each device only reaches the resources it truly needs. By enforcing least-privilege principles, organisations can minimise unnecessary communication paths.
This helps reduce the risk of lateral movement and limits the spread of threats within the network.
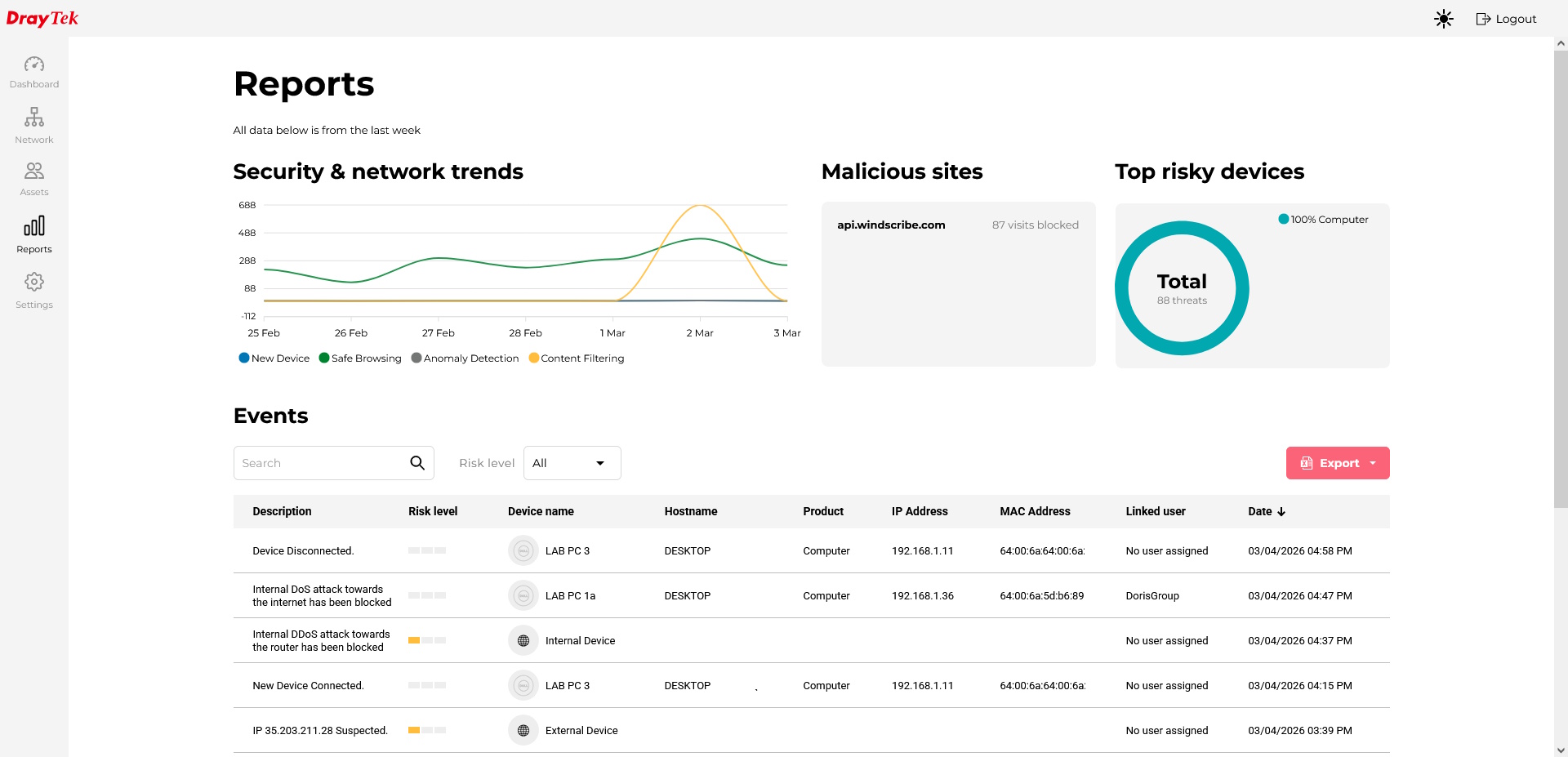
Actionable Reporting
Gain clear visibility into security events, alerts, and traffic activity through easy-to-read reports and centralised logs. Faster access to relevant information helps IT teams triage incidents more efficiently.
Built-in reporting also supports compliance and audit requirements without the need for additional monitoring tools.
Always-Current Defence
Stay protected against evolving threats with cloud-delivered security updates and continuously refreshed intelligence feeds. Protection policies and signatures remain current without manual updates.
This ensures your network benefits from the latest threat intelligence with minimal operational effort.

Faster Time-to-Protection
Deploy protection quickly across all LAN devices and traffic through a gateway-based security approach. There is no need to install software on each endpoint, making rollout faster and more consistent.
This is especially effective for branch offices, remote sites, and smaller environments where rapid deployment is critical.
Lower IT Overhead
Reduce the burden on IT teams with automated protection policies and fewer manual rule configurations. Intelligent threat detection helps minimise the need for constant tuning and day-to-day intervention.
This allows teams to focus on strategic priorities instead of routine maintenance tasks.

VigorShield Threat Protection Sentry
| UK Product Code | EAN | Subscription Type | Product Description |
|---|---|---|---|
| VS-TPS-1M-K | 4710484749185 | Sentry 1 Month Key | VigorShield Threat Protection Sentry AI-assisted Security Solution - 1 Month Key |
| VS-TPS-12M-K | 4711637180909 | Sentry 1 Year Key | VigorShield Threat Protection Sentry AI-assisted Security Solution - 12 Month Key |
| VS-TPS-36M-K | 4711637180923 | Sentry 3 Year Key | VigorShield Threat Protection Sentry AI-assisted Security Solution - 36 Month Key |
| VS-TPS-60M-K | 4711637180930 | Sentry 5 Year Key | VigorShield Threat Protection Sentry AI-assisted Security Solution - 60 Month Key |
Compatible Devices
| Threat Protection Sentry | Threat Protection Guardian |
|---|---|
 Vigor 2136ax Vigor 2136ax |
 Vigor 2867 Vigor 2867 |
 Vigor 2767 / Vigor 2767ax Vigor 2767 / Vigor 2767ax |
 Vigor 2928 Vigor 2928 |
Frequently Asked Questions
Threat Protection can be used with many DrayOS 5 routers including the Vigor 2136ax, Vigor 2767/2767ax, and Vigor 2867 / 2928. The up-to-date list is available here.
Threat Protection Sentry can monitor up to 100 devices. Threat Protection Guardian can support up to 200 devices.
Threat Protection (TP) Sentry offers protection to up to 100 devices connected to the SOHO DrayTek router such as the Vigor 2136 series. The TP Guardian is dedicated to larger networks of up to 200 devices and is compatible with more powerful routers. For product compatibility, click here
VigorShield offers one of the two options: URL IP Protection that helps with Web Content Filtering (WCF), and Threat Protection (TP) which offers more advanced AI-assisted security solution. Since TP package also supports WCF functionality, both products can't be enabled on the router at the same time.
Threat Protection is licensed based on the number of devices seen by the router. This is primarily tracked by unique MAC addresses, with each MAC address assigned an IP address on the network counting as one device. However, a Zigbee hub that manages multiple IoT devices would still be considered a single node, provided its child devices do not communicate directly with the router or use the IPv4 stack.
Yes, the demonstration for Threat Protection is available on request here: Threat Protection Contact